A report published on Monday by Chinese cybersecurity firm Qihoo 360 claims that the U.S. Central Intelligence Agency (CIA) conducted an 11-year-long cyberespionage operation aimed at China’s critical industries.
Qihoo’s research revolves around the Vault 7 files published in 2017 by WikiLeaks. The Vault 7 files include exploits and tools used by the CIA to target computers, routers, mobile devices, and IoT systems.
Other cybersecurity firms previously linked these tools and exploits to attacks launched by a threat group tracked as “Longhorn” and “The Lamberts” against entities in Europe, Asia and Africa. Qihoo said its own analysis revealed that many of the Vault 7 tools had been used to target Chinese organizations, even before the files were made public by WikiLeaks.
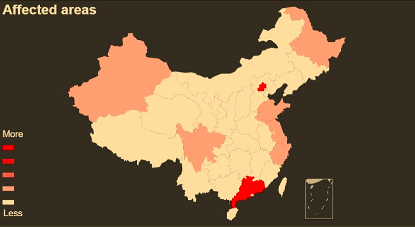
The targeted Chinese entities are said to include government agencies, scientific research institutions, internet companies, the petroleum sector, and aviation-related organizations, particularly in Beijing, Guangdong and Zhejiang. The Chinese company claims it’s aware of attacks launched by the CIA between September 2008 and June 2019.
“In the CIA’s attack against Chinese aviation organizations and scientific research institutions, we found that attackers mainly targeted system developers in these sectors to carry out the campaigns,” Qihoo said in an English-language blog post. “These developers are mainly engaged in works like information technology of civil aviation, such as flight control system, freight information services, settlement and distribution services, passenger information system, etc.”
The company added, “We speculate that in the past eleven years of infiltration attacks, CIA may have already grasped the most classified business information of China, even of many other countries in the world. It does not even rule out the possibility that now CIA is able to track down the real-time global flight status, passenger information, trade freight and other related information. If the guess is true, what unexpected things will CIA do if it has such confidential and important information? Get important figures‘ travel itinerary, and then pose political threats, or military suppression?”
The threat actor linked by Qihoo to the CIA — the company tracks it as APT-C-39 — reportedly used many of the tools contained in the Vault 7 leaks in its attacks, even before they were made public. The company said some of the “attack weapons” used by APT-C-39 are associated with the U.S. National Security Agency (NSA), which reportedly assisted the CIA in developing cyber weapons.
Another piece of evidence suggesting that the attacks were launched by hackers in the United States is related to the fact that the hacking tools were compiled during North American business hours.
Qihoo said its research showed that former CIA employee Joshua Adam Schulte created many of the agency’s “important hacking tools.”
Schulte worked for a CIA group that develops spying tools, but he left the agency on poor terms just months before the Vault 7 files were released. He has been charged by U.S. authorities for allegedly sharing many of the agency’s hacking tools with WikiLeaks. At the end of his trial on Monday, prosecutors portrayed Schulte as vindictive, but the defense denied the accusations and said the man had been scapegoated.
China has often been accused of conducting cyber operations, but Qihoo says it has discovered over 40 sophisticated hacking groups, including ones sponsored by nation states, targeting China. The company claims that its research actually shows that “China is one of the main victims of APT attacks.”
Related: The United States and China – A Different Kind of Cyberwar
Related: US Hacked Chinese Mobile Operators, Tsinghua University: Snowden















