California Governor Jerry Brown last week signed the country’s first Internet of Things (IoT) cybersecurity law, along with a controversial state-level net neutrality law.
The IoT cybersecurity law, SB-327, was introduced in February 2017 by Senator Hannah-Beth Jackson (D-Santa Barbara). SB-327 goes into effect on January 1, 2020, and it requires manufacturers of Internet-connected devices – such as TVs, phones, toys, household appliances and routers – to ensure that their products have “reasonable security features.” These security features should be able to protect sensitive customer information from unauthorized access.
“The lack of basic security features on internet connected devices undermines the privacy and security of California’s consumers, and allows hackers to turn everyday consumer electronics against us,” said Sen. Jackson. “SB 327 ensures that technology serves the people of California, and that security is not an afterthought but rather a key component of the design process.”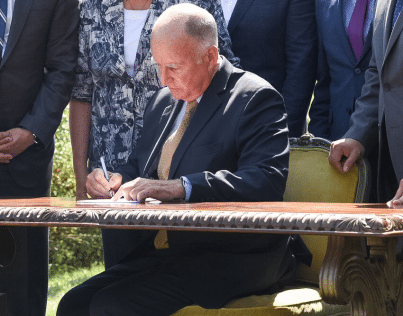
Veteran cybersecurity expert and cryptographer Bruce Schneier, who helped draft the IoT Cybersecurity Improvement Act of 2017, applauded the initiative, telling The Washington Post that it will “help everybody” even if “it probably doesn’t go far enough.” The IoT Cybersecurity Improvement Act of 2017, which could force security into IoT, has not made it past the Senate Committee on Homeland Security and Governmental Affairs.
Others have outright called the new SB 327 law “bad.” One of its biggest critics is Robert Graham of Errata Security, who described it as a “typically bad bill based on a superficial understanding of cybersecurity/hacking that will do little improve security, while doing a lot to impose costs and harm innovation.”
Gov. Brown last week also signed what have been described as the strictest net neutrality protections in the United States. Washington, Vermont and Oregon have also passed their own net neutrality regulations, and others will likely follow.
The Department of Justice claims the law, SB 822, is illegal. U.S. Attorney General Jeff Sessions argued that the Constitution prohibits states from regulating interstate commerce.
“Once again the California legislature has enacted an extreme and illegal state law attempting to frustrate federal policy. The Justice Department should not have to spend valuable time and resources to file this suit today, but we have a duty to defend the prerogatives of the federal government and protect our Constitutional order,” Sessions said.
Unsurprisingly, the representatives of U.S. telecoms companies also oppose the legislation.
“Broadband providers strongly support net neutrality, but SB 822 undercuts California’s long history as a vibrant catalyst for innovation and technology,” said Jonathan Spalter, President and CEO of broadband industry lobbying group USTelecom. “The internet must be governed by a single, uniform and consistent national policy framework, not state-by-state piecemeal approaches. Governor Brown should use his veto pen on this legislation, and Congress should step in to legislate and provide consumer protections that will resolve this issue once and for all.”
On the other hand, many activists and Internet freedom supporters praise California for the law.
“This victory in California is a testament to the power of the free and open Internet to defend itself. And it’s a beacon of hope for Internet users everywhere who are fighting for the basic right to express themselves and access information without cable and phone companies controlling what they can see and do online.” said Evan Greer, deputy director of Fight for the Future, a digital rights group that played an important role in passing SB 822.
“Despite their army of lobbyists and millions spent lining the pockets of legislators, these companies continue to lose ground in the face of overwhelming cross-partisan opposition to their greedy attacks on our Internet freedom. When all is said and done, Comcast, Verizon, and AT&T are going to wish they’d never picked a fight with Internet over net neutrality. Other states should follow California’s lead, and Congress should pass the joint resolution to reverse the FCC’s resoundingly unpopular repeal,” Greer added.
Related: Leveraging Segmentation to Secure IoT
Related: Addressing IoT Device Security Head-on
Related: Industrial Internet Consortium Develops New IoT Security Maturity Model
Related: The Path to Securing IoT Ecosystems Starts at the Network













