Attackers are doing a better job at hiding in the most complex parts of computer operating systems, according to a new report from FireEye-owned Mandiant.
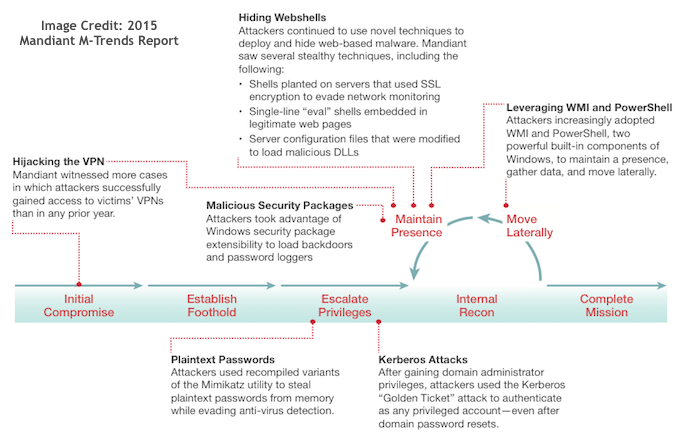
In its sixth annual Mandiant M-Trends report, the well-known breach investigations company found that more attackers are utilizing several complex tactics including using Windows Management Instrumentation (WMI) and PowerShell to avoid detection and carry out broad commands on compromised systems.
In the last six months of 2014, Mandiant saw an increase in attackers using PowerShell and WMI for post-compromise activity.
“Attackers are using built in components of Windows that are extremely powerful but relatively obscure in lieu of a lot of the things where attackers needed to previously use specialized tools or malware,” Ryan Kazanciyan, technical director at Mandiant, told SecurityWeek.
“They are not necessarily ways to infect a system from scratch, but they are ways that attackers can remain persistent in an environment and evade detection for a much longer period by using some of these advanced techniques,” he said.
In several incidents analyzed by Mandiant in 2014, attackers relied upon remote commands in PowerShell and in-memory scripts to move laterally and harvest credentials.
“In the past, moving laterally and executing commands in a typical Windows attack usually entailed a mix of built-in Windows utilities (such as net, at, and so on), custom malware, batch or Visual Basic (VB) scripts, and regular administration tools such as PsExec,” the report said. “These techniques were reliable and easy for attackers to use. But they also left behind telltale forensic artifacts and footprints.”
“Attackers are leveraging components of Windows that a lot of people users don’t know really exist or don’t understand how they work,” Kazanciyan said.
Mandiant said that more often than before, advanced persistent threat (APT) groups are using WMI and PowerShell to move laterally, harvest credentials, and search for useful information within Windows environments.
“It’s the natural escalation, I think, as attackers discover how they are getting caught and proactively decide to do things a little better,” Kazanciyan said.
“PowerShell code can execute in memory without ever touching disk on an accessed system, limiting any evidence. And older versions of PowerShell that are installed by default in typical environments cannot maintain a detailed audit trail of executed code,” the report explained.
Attackers are also using the WMI command line tool wmic.exe, which extends WMI’s capabilities to the shell and scripts.
“Attackers can use WMI to connect to remote systems, modify the registry, access event logs, and most important, execute commands. Aside from an initial logon event, remote WMI commands often leave little evidence on the accessed system,” the report said.
Additionally, Mandiant witnessed that widely available credential-stealing tools have made harvesting passwords and escalating privileges in a Windows environment much easier.
Throughout 2014, Mandiant experts found that targeted attackers typically used two techniques: “Pass-the-hash” to authenticate with stolen NTLM hashes, and using the freely available “Mimikatz” tool to recover plaintext passwords from memory.
Concerningly, Mandiant said that it did not see a single instance when a victims’ anti-virus software detected or blocked Mimikatz, despite the tool’s popularity.
Microsoft has reduced the effectiveness of these techniques in Windows Server 2012 R2 and Windows 8.1, Mandiant explained, but for most investigations it worked on last year, clients still relied on Server 2008 functional domains and Windows 7 endpoints.
Taking Defensive Action
While advanced threat actors continue to evolve their tools and tactics to reduce their attack footprint and remain undetected, Mandiant suggested a few actionable takeaways.
Enterprises should make sure that they maintain capabilities for both real-time monitoring and “look-back” forensics capabilities across endpoint systems, log sources, and network devices. Additionally, security teams should establish a “baseline of normal activity” in an environment while proactively scanning for deviations from that baseline.
Additional Findings
The report also found that organizations have made slight improvements in detecting breaches faster, but less than one third of organizations actually identified that they had been breached on their own. In 2014, only 31% of Mandiant’s customers discovered on their own that they were breached – down from 33% in 2013 and 37% in 2012.
Based on investigations conducted by the security firm throughout 2014, the median number of days that attackers were present on a victim’s network before being discovered dropped to 205 days in 2014 from 229 in 2013 and 243 in 2012.
In one extreme case, Mandiant said, a client that it worked with in 2014 had unknowingly been breached for more than eight years.
Other findings of interest include:
• Application virtualization servers as an entry point – Mandiant’s investigations found that while retailers’ virtual machines were sufficiently secured, they often failed to implement two-factor authentication, allowing a single stolen user credential to make their entire networks vulnerable.
• Threat actors impersonating the IT department – IT-posing phishing emails comprised 78% of observed phishing schemes witnessed by Mandiant in 2014 versus just 44% in 2013.
• Rise in e-commerce attacks where chip-and-pin (EMV) security is used to protect payment cards – Mandiant responded to more compromises of e-commerce companies and payment processors in countries that use chip-and-pin than it has in the past, suggesting increasing threats for e-commerce businesses in the U.S. as the nation begins to adopt the technology.
While the report did not provide hard statistics on the number of breach investigations used to compile the report, Kazanciyan told SecurityWeek that the number was “in the hundreds” with a majority of those being Fortune 500 or Fortune 1000 firms.
“Based on the incidents that Mandiant investigated in 2014, threat actors have continued to evolve, up their game, and utilize new tools and tactics to compromise organizations, steal data and cover their tracks,” Kevin Mandia, SVP and COO at FireEye, said in a statement.
“No security is perfect. No one can predict every new intrusion technique. And as we continued to see in 2014, no threat group is going to close up shop just because they’ve been thwarted by a new security tool,” the report concluded.
Mandiant’s 28-page report is based on actual high profile, real-world incidents vs. surveys and should be required reading for security professionals of all levels.
The full report, “M-Trends 2015: A View from the Front Lines” is available online.














