Arbor Networks, a provider of DDoS and threat protection solutions, announced on Monday that they have collaborated with Google Ideas to create a data visualization that maps global distributed denial of service (DDoS) attacks.
Google Ideas is an initiative that explores how technology can enable people to confront threats in the face of conflict, instability or repression.
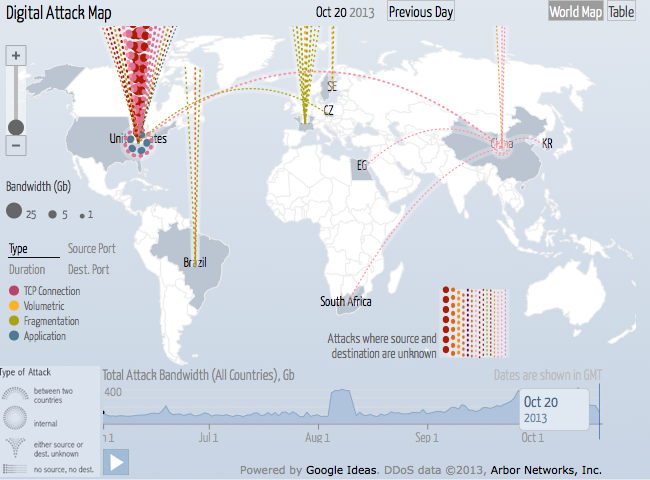
According to the announcement, Google Ideas uses anonymous data from Arbor Networks’ threat monitoring system to build a data visualization that allows users to explore historical trends in DDoS attacks, and make the connection to related news events on any given day. The data is updated daily, and historical data can be viewed for all countries.
“This collaboration brings life to the ATLAS data we leverage every day to uncover new attack trends and techniques, sharing it in a visual way that connects the dots between current events and cyberattacks taking place all over the world,” Dan Holden Director of, Arbor’s Security Engineering and Response Team, wrote in a blog post.
Online a DigitalAttackMap.com, the project was introduced at the ‘Conflict in a Connected World’ summit, hosted by Google Ideas, in partnership with the Council on Foreign Relations and the Gen Next Foundation. The summit brings together experts, technologists and people with relevant experience from across a wide range of disciplines and backgrounds to address how technology can play a role in exploring trends, exposing threats and empowering people in conflict.
When Arbor Networks first began working with network operators in 2000, flood attacks were in the 400Mb/sec range. Today, they regularly exceed 100Gb/sec, the company said.
“Beginning in 2010, and driven in no small part by the rise of Hacktivism, we’ve seen a renaissance in DDoS attacks that has led to innovation in the areas of tools, targets and techniques,” Arbor Networks explained. “Today, DDoS is a complex threat that mixes flood, application and infrastructure attacks in a single, blended attack.”
“The people at Google Ideas have really done an amazing job bringing Arbor’s global DDoS attack data to life,” said Arbor Networks President Colin Doherty. “The goal of this collaboration was to show what a global threat DDoS is and how DDoS can be used to suppress speech and threaten open access to information.”















