Simurgh, a privacy tool used in Iran and Syria to bypass Internet censorship and governmental monitoring, is being circulated with a backdoor. The compromised version has been offered on P2P networks and via web searches. Research conducted by CitizenLab.org has shown that malicious version isn’t available form the original software source, only through third-party access, so it appears that Simurgh has been repackaged.
Last week, Morgan Marquis-Boire, on the CitizenLab.org blog, broke the news about the malicious version of the software. His research detected a major red flag between the two versions, namely the installation process.
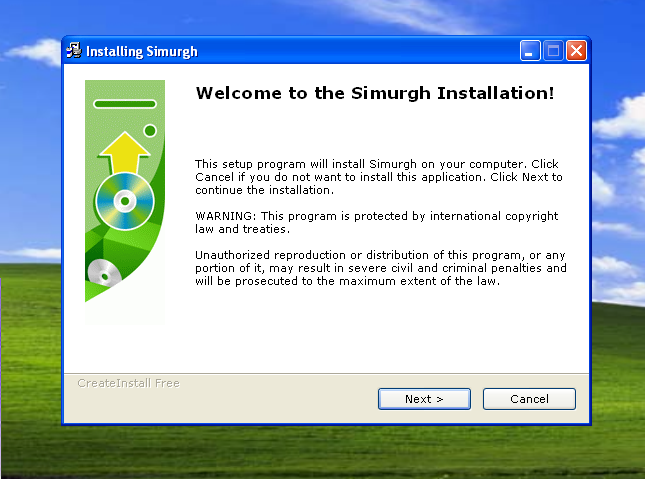
The legit installation screen looks like this:

However, the compromised version will present the screen below:
The troubling aspect of the malicious version is that it does install the proxy as expected, however it adds a keylogging component, and ships the recorded information off to a server hosted in the U.S. and registered to a person in Saudi Arabia.
In response to this attack, the team that develops Simurgh has instituted a check that will warn the user if they are running a compromised version of the software. In addition, they have published the MD5 values of the legitimate installation file, and started spreading warnings about the rogue version. Security firm Sophos confirmed CitizenLab’s findings.
In a blog post, Chester Wisniewski noted that, “this malware is targeting users for whom having their communications compromised could result in imprisonment or worse.”
“Many thousands of people depend on the legitimate Simurgh service, which makes it likely that far more people have been impacted by this malware.”
At present, it is unknown who developed the hijacked version of Simurgh, or why they did so. We can only assume the worst.
Related Reading: Who Watches the Watchers?
Related Reading: ‘Internet Kill Switch’ – Is this Technically Feasible in the US?














