Update: NetQin Mobile reached out to SecurityWeek to let us know that they had previously identified the same malware under the name AnserverBot on September 19th. Dr. XuXian Jiang, Chief Scientist at NetQin’s US Security Research Center, offers a detailed report on how the malware works. – Editor
Researchers at Trend Micro have discovered a unique feature circulating in some Android-based malware. The malicious application is using a blog in China to act as a Command and Control (C&C) server.
Over the last year, rogue Android applications have made headlines, and stressed to consumers the need to stick with known Application repositories, such as the Android Marketplace. On Tuesday, Trend Micro discovered a malicious Android application out of China using a new trick to receive instructions.
“This, based on our research, is the first time Android malware implemented this kind of technique to communicate with its server,” commented Trend’s Karl Dominguez, a Threat Response Engineer.
Disguised as a eBook reader, the application requests nearly total control over the mobile device when installed, including access to the Web, network settings, the ability to edit, read, and receive SMS or MMS messages, read and write to contact lists, disable key locks, make calls, and more.
“From our analysis, we found that this malware has two hard-coded C&C Servers to which it connects to receive commands and deliver payloads. The first server is just like the usual remote site, where the malware posts and gets information and commands. The second C&C server, however, caught our attention. The second C&C server is a blog site with encrypted content,” Dominguez notes.
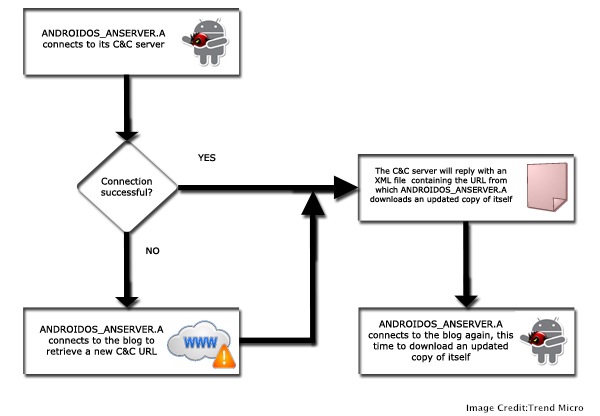
The malware will connect to the C&C, which replies with a XML file containing the download URL to obtain updated code. Checking the development history on the blog shows that updates focused on creative messages that tricked users into allowing application updates. If the initial C&C contact fails, the malware will check the blog for a new URL, and continue the update process.
“The use of blog platforms in malware activities is not unheard of for malware affecting computers. In fact, early this year a botnet was found using Twitter for issuing commands to affected systems,” Dominguez noted. “If anything, this recent adaptation of mobile malware using this technique is another sign of its continued development and proliferation.”
Again, the easiest way to avoid problems with malicious applications is to avoid downloading generic knock-offs, and to stick to the known, trusted marketplaces.
Related Reading: Mitigation of Security Vulnerabilities on Android & Other Open Handset Platforms















