Jericho Botnet Analysis: Infection, Persistence and Malicious Functions
We’ve talked a lot about modern malware as a concept, but I’d like to use this week’s column to call out one particular sample of malware that I’ve had my eye on for the last several weeks – a new banking botnet that has been referred to as the Jericho Botnet.
This botnet also illustrates the importance of the malware trends for 2012 that I called out in an earlier column – the increasing sophistication of malware writers’ coding techniques, the need to more tightly control applications that malware will use to communicate with the outside world and the advantages of sandbox analysis when applied to anti-malware network security.
We’ll also analyze how this botnet typified a piece of “modern malware” by focusing on three of the stages of the malware lifecycle we outlined in an earlier post, The Evolution of Malware: Infection, Persistence and Malicious Functions.
Infection: How is the malware delivered?
In early April we began to detect samples of a new banking botnet that was hitting enterprise networks, and showing very low coverage rates by traditional antivirus signatures. We detected these samples using sandbox analysis techniques discussed earlier to scan unknown files for behavior consistent with that of modern malware. On closer inspection, these malicious files appeared to be based on a variant of the well-known, stealthy Jorik Trojan, and we noticed that all 42 variants were originating from Israeli Internet space.
These files were delivered to victims via .php pages during browsing sessions. Despite originating from domains located in Israel, analysis of the malware package itself showed that the vast majority of the URLs used to deliver the malware ended in ierihon(dot)com. Ierihon is the word for Jericho in Romania (hence the name), and reverse engineering of the sample revealed several other Romanian words buried in the sample. All of this suggests a Romanian origin for the malware package.
Persistence: How does it disable antivirus? Does it install backdoors?
The most interesting characteristic of the Jericho botnet as an example of modern malware is the pains that the malware writers went to avoid detection by antivirus programs. One of the main techniques employed was leveraging the communications processes of other applications as a way of hiding its communications and other activities. The developers also appeared to be making use of rapid iterations of their software, changing the malware’s profile enough that there was some time lag between the latest malware release and when AV signatures were updated to detect the threat.
To begin with, on a system whose AV software is not able to identify the initial infection, the malware is able to inject itself into the Windows logon to maintain its presence on the infected host after a reboot. This is how Jericho establishes an initial toehold on the target system. From there, the malware uses the technique of hooking into specific processes from common applications. The malware showed a heavy preference for targeting Firefox, but other browsers like IE, Chrome and Opera were used as well. Other web-facing applications and common software libraries leveraged by Jericho to perform its malicious functions included: Java, Outlook and even Skype, proving that locking down the browser is definitely not enough to combat a modern malware threat. This enables the malware to hide its activities within approved applications during run time, and also makes it significantly harder for security solutions to analyze the malware via traditional Windows calls. Again, this potentially avoids drawing unwanted attention from antivirus programs and increases the malware’s resilience in the face of network and endpoint defenses.
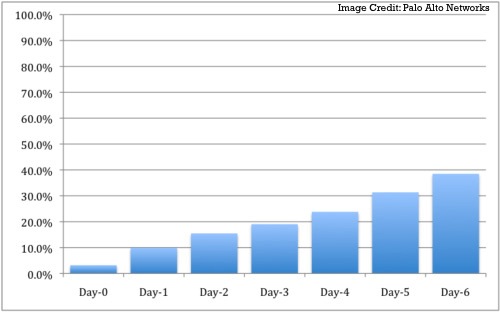
A longitudinal analysis confirms that this combination of piggybacking on common applications (another trend for 2012) and a rapid-iteration malware variants was able to avoid the scrutiny of most antivirus programs over multiple days. In fact, of the 42 samples of Jericho we analyzed, the top AV solutions only achieved a 3.2 percent detection rate on the day the sample was first detected in the wild. AV coverage seemed to slowly, but steadily improve over time, with overall coverage improving to a 39 percent detection rate over seven days. However, 12 of the 42 (roughly 30 percent) of the Jericho signatures were not detected at all over a seven-day period by any leading AV solution.
Malicious Functions
Once Jericho has leveraged third party applications, what does it do? It uses these applications to find and steal passwords as well as cookies, which allow the attackers to break into a victim’s online accounts. Disassembly of the samples revealed well over 100 domains that are targeted with the vast majority belonging to banking and other financial websites. As a result, it seems fairly apparent that the core goal of this botnet is related to financial theft.
The Silver Lining
It’s worth calling out again that the rapid sophistication of malware over the last several years is a byproduct of the network effect: malware writers are now able co-opt increasingly powerful end-user applications and then analyze the effectiveness of their own efforts vis-à-vis existing IT security products and share knowledge about which evasive techniques work and which ones do not. This is why I expect more malware will leverage trusted applications in the near future. All is not FUD, however, as modern IT security products are increasingly able to collect malware samples from many different points and analyze the behavior of these files in a centralized sandbox environment (the network effect on the IT security site), malware identification and code analysis will become significantly easier.
















