One of the Windows zero-day vulnerabilities patched by Microsoft this month has been exploited by cybercriminals since last summer, Trend Micro said on Friday.
Microsoft fixed many vulnerabilities with the March 2017 Patch Tuesday updates, including three flaws that had been exploited in the wild before patches were made available.
One of the flaws, tracked as CVE-2017-0022, has been described as an XML Core Services information disclosure vulnerability that can be exploited through Internet Explorer by getting the targeted user to click on a specially crafted link.
“An information vulnerability exists when Microsoft XML Core Services (MSXML) improperly handles objects in memory. Successful exploitation of the vulnerability could allow the attacker to test for the presence of files on disk,” Microsoft said in its advisory.
The security hole was spotted by researchers at Trend Micro, which reported it to Microsoft in September, and Proofpoint.
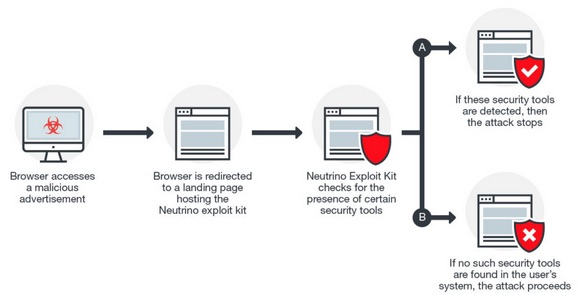
According to Trend Micro, the zero-day flaw has been used in the AdGholas malvertising campaign since July 2016, and it was added to the Neutrino exploit kit in September 2016. Experts believe CVE-2017-0022 replaced CVE-2016-3298 and CVE-2016-3351, which had also been used by AdGholas and another actor in malvertising operations before patches were made available.
Experts revealed a few months ago that CVE-2016-3298 and CVE-2016-3351 had been leveraged by the cybercriminals to avoid researchers. CVE-2017-0022 was apparently used for similar purposes.
“Successful exploitation of this vulnerability could allow a cybercriminal access to information on the files found in the user’s system,” explained Trend Micro threat analysts Brooks Li and Henry Li. “In particular, the attacker would be able to detect if the system is using specific security solutions – especially ones that analyze malware.”
Trend Micro has made available a technical analysis of the vulnerability and Microsoft’s patch. The company has also provided a brief explanation of how CVE-2017-0022 is exploited in a malvertising campaign involving the Neutrino exploit kit:
Related: Massive Stealthy Malvertising Campaign Uncovered
Related: Malvertising Jumped 132% in 2016














