From Security Products to Security Systems, and Now: Security Networks
We all know that servers virtualization technologies have matured already and many networks adapt them in order to more efficiently meet today’s business needs.
With the Software Defined Networking trends and NFV (Network Function Virtualization) initiative that proposes a design approach for building complex IT applications, we see a similar process of adapting network technologies to be more business efficient well. These technological movements in the IT infrastructure created potential for rapid innovation in network and application security.
On the other hand, security challenges have significantly increased as well. Focusing more on availability-based attacks, as seen in the figure below, the security friction surfaces are now wider than ever, and much more dynamic for enterprises, cloud service providers and carrier organizations:
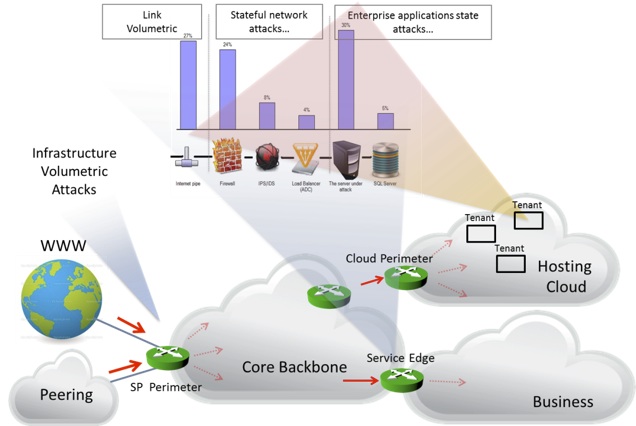
• The service providers peering points (SP perimeter) are under volumetric DDoS attack threats which have the potential to disrupt their overall operations and customer services.
• The enterprises’ businesses networks service edges are under the threat of multi-vector attacks, which aim to saturate the business internet pipe, misuse the resources of the internal network’s stateful elements (e.g., firewalls, load balancers, intrusion prevention devices) through network state attacks and misuse the business application resources through various state-based applications.
• The cloud hosting perimeter become much more complex as the security friction surface is now multiplied by the number of internally hosted “business tenants”, while each tenant is actually exposed to the same multi-vector attack described above.
The following illustrates an even bigger problem at the cloud:
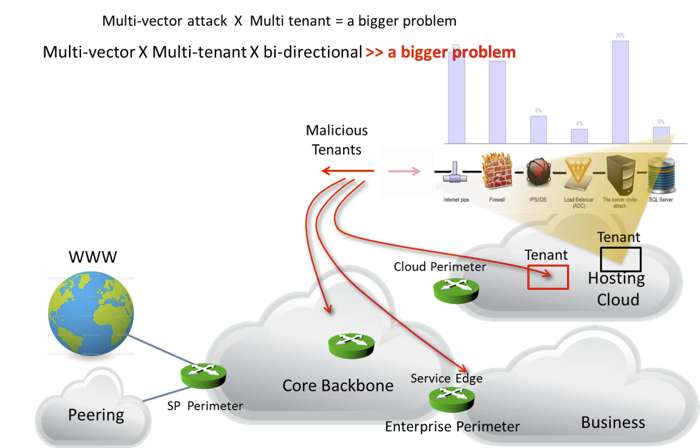
• An attack on one tenant can impact the entire cloud infrastructure and any other tenant (especially if it is a network volumetric one).
• The new security friction surface now becomes much more complex to control as the number of tenants can reach an enormous number, their resources are usually virtualized (dynamic and elastic) and each tenant can be transformed into a “malicious tenant” or a network of malicious tenants, and start attacking the tenants at the same cloud, on other business networks and at the carrier network itself.
Looking at the above, I don’t think there is any doubt that there is a need, now more than ever, to present a holistic solution approach to this problem. Holistic in the sense that the network itself needs to be part of the security service allowing:
• Security monitoring capabilities at various network points that can adapt and change their characteristics per potential risk
• A security control system that will provide a situation awareness in a very wide sense based on these monitoring inputs
• Network mitigation capabilities that will allow the network itself to be “programmed” to act against and according to the risk .e.g., quarantine infected tenants, deploy distributed ACLs, isolate network tenant’s routes, redirect suspicious traffic into security scrubbing centers and more.
So, although the security threats and the complexity in controlling them has become much more challenging than before, the same technologies (cloud virtual environments, network virtualization and software defined networks) that really contribute to this complexity, are also the technologies that potentially need to be used for solving it.
Security applications that will know how to use the new programmable nature of the servers and network virtual environments are key for these solutions. The old approach of just deploying more and more security devices and systems as part of the network data-plane will probably be much more expensive and will not do the job. The time has come for Attack Mitigation Adaptive Networks.














