In part one of the Virtualized Data Center Security series, I wrote about how important it is to ensure security solutions are integrated with orchestration systems so that security does not slow down the dynamic nature of virtualization and cloud environments. In part two, I continued the discussion on security requirements beyond automation and orchestration, addressing the question: what stays the same and what changes as you move towards virtualization and cloud?
In this week’s column, I address the choice between physical and virtualized firewalls, and which form factor is ideal depending on your environment. Many organizations looking at security for virtualized and cloud environments automatically assume that it is a choice between one or the other. I think the answer may vary based on your architecture, but there is a place for both.
The Need for Virtualized Firewalls
Let’s first start with the use case for a virtualized firewall. In figure 1 below, take a look at the scenarios depicted in (A) and (B). Assume in your virtualized data center environment, you’ve segmented your data center by application tiers- application, web and database. In (A) you’ve maintained the same application trust levels on the same server. In (B), you’ve mixed the application trust levels.
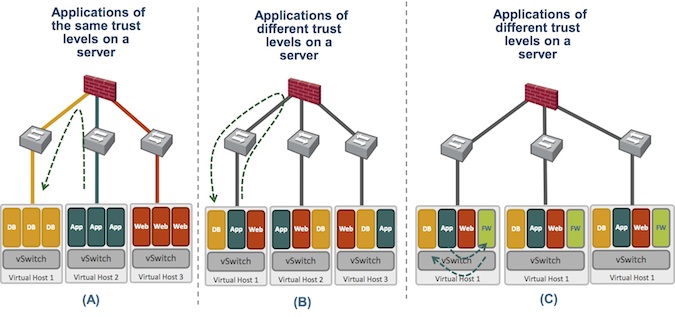 Figure 1
Figure 1
In scenario (A), traffic is going from the application to the database, i.e. Microsoft Sharepoint to the SQL server, and each application tier resides in its own VLAN. Traffic can be routed via the virtual switch (vSwitch) northbound to the external switching fabric and external firewall.
This same option could be utilized in option (B) but is probably not ideal. Most of the traffic in (B) is East-West communications, and forcing traffic Northbound through a physical firewall is very inefficient and expensive due to the number of physical ports required to service the VM traffic. Each application within the virtual server would need to be in its own VLAN to horseshoe the traffic from the application VM to database VM. Therefore, a virtualized firewall would be preferable for intra-host inspection instead of the physical firewall, as shown in the scenario (C).
However, there are several considerations of the virtualized firewall that are critical. A virtualized firewall that cannot benefit from hardware acceleration is unlikely to deliver the same level of performance as a physical firewall. But, the software architecture will make a difference, so it is critical to consider virtualized firewalls with software architectures that optimize performance and reduces latency.
It is also important to understand what features are supported by virtualized firewalls in this environment. In the last couple of years, the virtualized network security offering has proliferated. Many vendors, in an effort to participate in the “virtualization and cloud buzz” just repackage their physical firewalls in a virtual form factor without consideration for the requirements in a virtualized environment. Specifically, security policies should track virtual machine creation or movement, and should support orchestration to automate the currently manual process of policy changes.
At the other end of the spectrum, you have virtualization platform vendors with virtualized security appliances that understand the dynamic nature of the environment, but do not offer the appropriate security functions. Modern threats to the network don’t go away just because you virtualized your environment. Attackers are using new, targeted, sophisticated and coordinated techniques like exploits, malware, and spyware to breach your network. Your application developers are deploying applications and leveraging open ports on the firewall to bypass security. Partners, contractors and mobile users need access to your applications no matter where they are. It is therefore important for virtualized firewalls to understand applications beyond ports and protocol, support user-based policies, and incorporate a complete threat framework to deal with modern threats.
How do you optimize for both? You need virtualized next-generation firewalls that already tackle the challenge of safe application enablement, yet are dynamic enough to understand virtual machine movement, and can integrate with orchestration software.
Will Virtualized Firewalls Replace Physical Firewalls?
Will virtualized firewalls take over and replace all of your physical firewalls in the data center then? No. Because of the stringent performance requirements in the data center, physical firewalls will not go away. In some environments, they may be the only choice. In others, they may be used for edge/perimeter data center filtering because of the throughput needed. In most hybrid environments, a combination of physical and virtualized firewalls will be deployed. The physical firewall segments between virtualized servers, so the right sets of users are accessing the virtualized servers. Meanwhile, the virtualized firewall delivers segmentation within the server, as shown in Figure 2.
Another useful benefit of this architecture is that the physical firewalls protecting the virtualized servers can now also defend against hypervisor vulnerabilities. Protecting against hypervisor attacks requires hypervisor integrity and software hardening by your virtualization vendor. But, complementary security that provides appropriate access to the hypervisor and inspects for virtualization platform vulnerabilities is crucial. This cannot be achieved by the firewall within the server itself. After all, if you already have access to the hypervisor via an attack, you control the entire server.
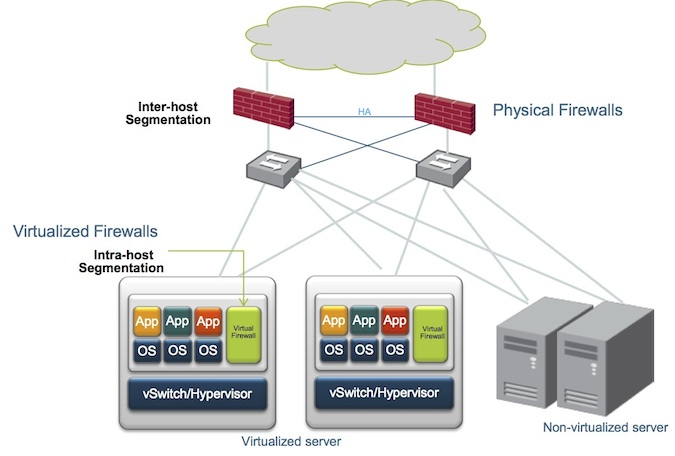
Figure 2
Summary
In summary, the data center environment is moving towards automated, dynamic, on-demand services. Security architectures must keep up with these changing requirements, but must also deal with the realities of threat protection and safe application enablement challenges that never went away. In short, network security for virtualized data center and cloud environments should:
• Deliver all security features that are table stakes (safe application enablement, threat protection, flexible networking integration)
• Become more dynamic:
– Security policies must track VM instantiation, and movement
– Security policies must be orchestrated
• Deliver consistent, centralized, management for all security appliances in the data center (physical, hybrid or mixed)
This concludes the multi-part Virtualized Data Center Security Series. If you are looking at or have deployed security for your virtualized data center, do share your thoughts on your architectural considerations.














