By Using a True Security Zone, Defenders Can Take Initiative Away From the Enemy and Shift the Success of Close Battle in Their Favor.
According to US military doctrine, a demilitarized zone or DMZ is an area devoid of military forces. It is designed to separate opposing forces to prevent hostile actions. Yet it is the term that cyber security practitioners have been using for years to describe the place on our network where we most often engage our cyber enemies.
The DMZ in most networks is segmented from the majority of the enterprise through a firewall. It normally hosts online web services accessible by remote users and customers. A cyber DMZ is the first layer of defense into a network and is anything but demilitarized. In this article, I offer an alternative approach for security professionals to contend with this space. I will introduce the concept of a security zone within the cyber area of operations.
 The US Army Operations Field Manual 3-90 defines a security zone as the “Area that begins at the forward area of the battlefield and extends as far to the front and flanks as security forces are deployed. Forces in the security area furnish information on the enemy and delay, deceive, and disrupt the enemy and conduct counterreconnaissance.” It further defines purpose of the operations in the security area “to provide early and accurate warning of enemy operations, to provide the force being protected with time and maneuver space within which to react to the enemy, and to develop the situation to allow the commander to effectively use the protected force.”
The US Army Operations Field Manual 3-90 defines a security zone as the “Area that begins at the forward area of the battlefield and extends as far to the front and flanks as security forces are deployed. Forces in the security area furnish information on the enemy and delay, deceive, and disrupt the enemy and conduct counterreconnaissance.” It further defines purpose of the operations in the security area “to provide early and accurate warning of enemy operations, to provide the force being protected with time and maneuver space within which to react to the enemy, and to develop the situation to allow the commander to effectively use the protected force.”
As shown in Figure 1, the Security Zone is a component of defense in depth through the battlespace. It is an area to which a commander can assign responsibility and specific tasks. In this way, he provides focus to his subordinates and allows for mutual support between elements. Although linear battlefields are not as prevalent in combat operations today, I would argue that networks are very linear in nature. And even though a mobile workforce and their supporting devices are a factor to contend with, the topology of the network can be designed to preserve defense in depth. This simplistic battlefield model will serve as a basis to begin the discussion on a complex topic.
Figure 1: Basic Military Operations Battlefield Management
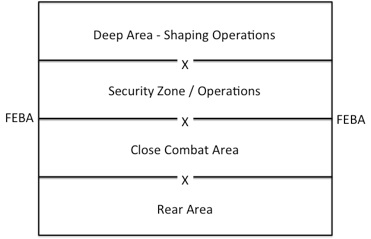
Figure 2 depicts the translation of this military concept to practice within network defense. Again this is a simplistic depiction of a network, but it is illustrates the concept well.
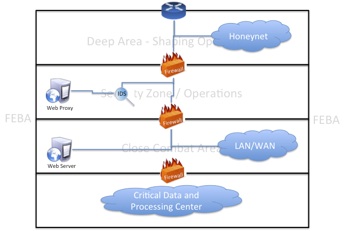
Figure 2: Military Graphics with Basic Network Security Overlay
As shown, firewalls, intrusion protection systems and web proxies are some of the tools in the security area to identify enemy reconnaissance attempts to protect the network and give time to react.
In military operations, security zone operations are some of the most complex that can be undertaken. First, the primary mission is counterreconnaissance. In other words, you work to identify and eliminate the most clandestine efforts the enemy has to find you and pinpoint your key assets. Second, security operations are normally an economy of force mission. This means that the limited forces combined in use to maximum effect. Traditionally, this mission has been reserved for modern Cavalry units. These units are typically elite, very well trained and have the best weapons platforms available. Third, they must also coordinate and rely on assets outside of their organization for success to include higher echelon formations, national level intelligence and close air support from a variety of aerial platforms. In most cases, the winner of the counterreconnaissance fight wins the battle because they will have the upper hand in understanding what is happening on the battlefield.
As it relates to cyber, the security zone is the ideal region to locate and destroy enemy scans and probes. If shaping operations are successful, most of these attempts should be redirected to honeynets/pots, blackholes or through other techniques to obfuscate the network and supporting activities. A network defender should assign a team or in some cases an individual to fight the security zone battle. That team will focus their efforts on locating threat reconnaissance techniques by starting with their Intelligence Preparation of the Operational Environment. Their resources should include external sensors and log files and external threat intelligence to understand capability, intent and adjacent activity. This information will inform the team to think like the threat and determine the best counter to their actions. Knowing the type of attack will allow the counter recon efforts to tune their technology to detect recon attempts and defeat them in the security zone. The team must have a strong understanding of port and protocol scanning tools and subsequent signatures must be used to identify recon activity.
The security force must also work “on net” to purposefully look for signs and symptoms of threat activity. It must also have the authority within any organization to kill or minimally “cage” identified malicious behavior. A vulnerable friendly asset can be turned into an enemy asset, so the team must be provided rules of engagement of how to handle that threat. This team must also be able to determine what information about the configurations, operating systems, topology, technology associated with an enterprise is available through open source research and work to obfuscate or eliminate that data from being leaked.
As discussed in previous articles, just having the people or technology to defend a network is not good enough. By using a true security zone as part of a defense in depth strategy, network defenders can begin to take initiative away from the enemy, defeat enemy reconnaissance efforts and shift the success of close battle in their favor.














