A couple of researchers claim they have earned $50,000 from Apple for finding some serious vulnerabilities that gave them access to the tech giant’s servers.
Harsh Jaiswal and Rahul Maini, India-based bug bounty hunters who specialize in application security, said they discovered the flaws in recent months, being inspired by a group of researchers who in October reported receiving hundreds of thousands of dollars from Apple for a total of 55 vulnerabilities, including ones that exposed source code, iCloud accounts, warehouse software, and employee and customer apps.
Jaiswal and Maini said their research focused on Apple hosts running a content management system (CMS) powered by Lucee, an open source scripting language designed for developing web applications.
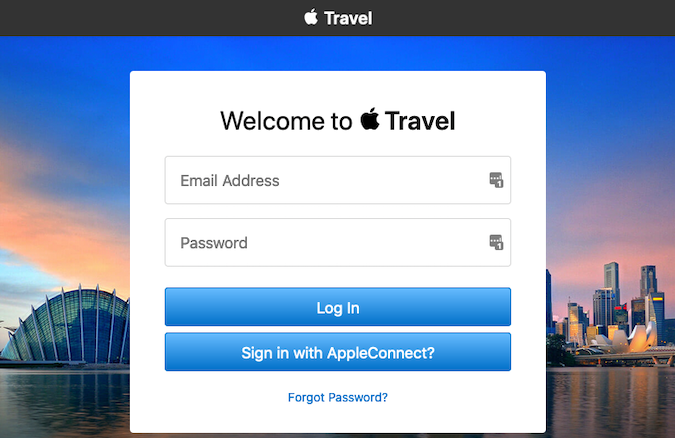
During their analysis, they discovered three Apple hosts that exposed the Lucee admin panel, including two apparently associated with a travel portal provided by Apple to employees. The portal is only accessible to users with valid credentials.
The researchers discovered a Lucee misconfiguration that gave them access to files without being authenticated, which ultimately allowed them to create a webshell on Apple servers and execute arbitrary code. They managed to conduct their tests without triggering Apple’s web application firewall.
Jaiswal and Maini said Apple decided to award them a $50,000 bug bounty after being informed about the vulnerabilities. Lucee developers were also contacted and they also took some steps to prevent these types of attacks.
“Apple promptly fixed the issue but requested us to not disclose the issue before they make some other changes,” the researchers said.
A detailed technical writeup describing the analysis process and the researchers’ findings was published last week.
Related: Apple Patches Three Actively Exploited Vulnerabilities
Related: Researcher Claims Apple Paid $100,000 for ‘Sign in With Apple’ Vulnerability
Related: Apple Patches Tens of Code Execution Vulnerabilities in macOS
Related: Apple Offers Hackable iPhones to Security Researchers














