iTunes Users Targeted in Massive Phishing Attack
Updated – 12:25AM 10/5/2010
Following a massive campaign targeting LinkedIn users last week, PandaLabs reported that Apple’s popular iTunes platform has become a major target for hackers looking to steal credit card data from the service’s millions of users. Cisco Security Researcher Henry Stern said in an email to SecurityWeek that this attack appears to be conducted by the same botnet as last week’s LinkedIn attack.
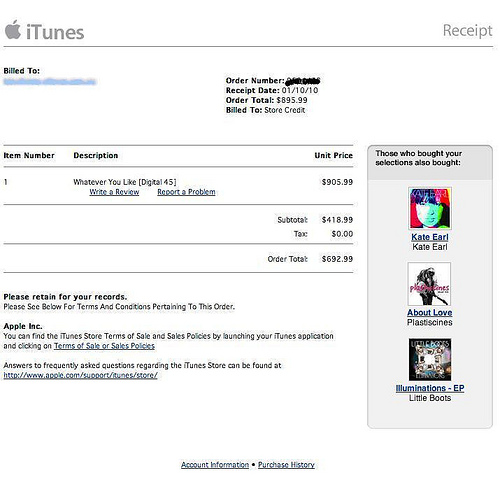
In this case, victims have been receiving emails informing users that they have made an expensive purchase on iTunes. The emails contain a subject line containing a randomized 12-digit fake iTunes order confirmation number. The user, having never made the purchase to begin with, is concerned by the email and naturally tries to resolve the problem – in this case by clicking on the fake link.
After clicking the link, the victim is asked to download a fake PDF reader. Once installation is complete, the user is redirected to an infected Web page containing the Zeus Trojan, which is specifically designed to steal personal data.
ZeuS, also known as Zbot, WSNPOEM, NTOS and PRG, is the most prevalent banking malware platform for online fraud, and has been licensed by numerous criminal organizations. The program then waits for the user to log onto a list of targeted banks and financial institutions, and then steals login credentials and other data which are immediately sent to a remote server hosted by cybercriminals. It can also modify, in a user’s browser, the genuine web pages from a bank’s web servers to ask for personal information such as payment card number and PIN, one time passwords, etc. A new variant recently emerged that targets mobile devices – ZeuS in the Mobile or “Ztimo”- used to overcome two-factor authentication.
Last week, the FBI, working in partnership with international law enforcement, busted several cybercriminals that targeted small- to medium-sized companies, municipalities, churches, and individuals, infecting their computers with ZeuS. The FBI reports that the group attempted to steal up to $220 million, successfully grabbing $70 million from victims’ bank accounts.
Cisco’s Security Division was able to provide some insight on the size and volume of emails being sent as part of the attack targeting iTunes users. Cisco’s Henry Stern suggested that the gap in the chart where activity drops off is likely due to a spam run completing and the botmaster starting a new one shortly before 10:30AM on Saturday.
An analysis of the email header is below:
From: iTunes Store
Subject: Your receipt #155562898256
Date: October 1, 2010 11:01:10 PM GMT+08:00
To: YourName
Delivered-To: your-email.address
Received: by 10.216.237.150 with SMTP id y22cs208673weq; Fri, 1 Oct 2010 07:04:49 -0700 (PDT)
Received: by 10.142.203.16 with SMTP id a16mr4707302wfg.213.1285941888137; Fri, 01 Oct 2010 07:04:48 -0700 (PDT)
Received: from email.address.com ([0.0.0.0]) by mx.google.com with ESMTP id 13si2771198wfg.81.2010.10.01.07.04.46; Fri, 01 Oct 2010 07:04:48 -0700 (PDT)
Received: from KVSCHALD (unknown [180.215.161.77]) by email.address.com (AntiSpam Platform) with ESMTP id 58C5ED8A2DC43D37 for ; Fri, 1 Oct 2010 22:04:25 +0800 (MYT)
Received: from badger1402.apple.com (badger1402.apple.com [17.254.6.185]) by mail.romanmfg.com with SMTP id A993453C8F8 for ; Fri, 1 Oct 2010 07:01:10 -0800















