Several pieces of malware and adware have been observed using a clever technique to hide the changes they make to the DNS settings of infected devices, ESET reported on Thursday.
One of these threats is DNS Unlocker, a piece of adware that ESET has classified as a potentially unwanted application (PUA). DNS Unlocker changes the settings of an infected computer so that it uses rogue DNS servers that inject malicious JavaScript code. This allows its operators to replace regular ads served by Google with their own ads and make a profit.
DNS Unlocker has been around for some time and there are several articles online on how to get rid of it. For example, one post published on Microsoft’s community forum in August 2015 advises users affected by the adware to manually configure IPv4 properties in the Windows control panel so that the DNS server address is obtained automatically.
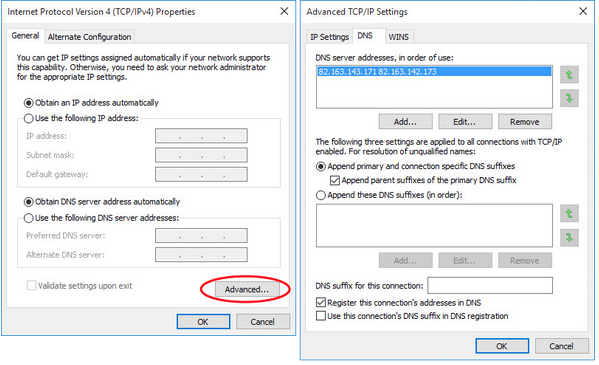
However, this piece of advice no longer works with more recent versions of DNS Unlocker. According to ESET, if a newer version is installed, users who access IPv4 properties in the control panel see that their DNS is obtained automatically.
Researchers discovered that the adware hides the changes from users by making modifications in the registry, where each network adapter has an entry called NameServer. The value of this entry contains the DNS server’s IP address when users set a static DNS.
When two static DNS addresses are set by the user via the control panel or the netsh command, they are stored in the registry as a list where each entry is separated by a comma (e.g. 192.168.1.21,192.168.1.22). Static DNS addresses can be manually added in the registry, but the modification is not shown in the control panel if the comma is replaced by a space (e.g. 192.168.1.21 192.168.1.22). If the ipconfig /all command is used to check the network settings, the static DNS address is displayed, but users are informed that the address is obtained automatically.
Adding the DNS addresses manually to the registry with a space between them allows attackers to hijack DNS settings without leaving an apparent trace. ESET pointed out that this could be a major problem for regular users and companies that offer remote support.
There is another method that can be used to identify and remove the rogue DNS addresses besides accessing the registry directly. In the IPv4 properties window, in the advanced settings section, the DNS server addresses are listed next to each other separated by a space, just like in the registry, but they should normally be listed one under another. Users can remove the rogue entries from this menu and their DNS server’s address will once again be obtained automatically.
ESET reported the issue to Microsoft on May 10. The company admitted that it’s a problem and it might consider making some changes in future versions of Windows, but it’s not treating it as a security flaw.
“As modifying the registry requires administrative privileges we do not consider this to meet the bar for security servicing through MSRC,” Microsoft said.
ESET noted that DNS Unlocker has been using this method in the wild since December 2015. The security firm discovered another piece of adware and two Trojans that leverage the same technique.
Researchers said the technique works on all versions of Windows, and it works even if the comma is replaced with a semicolon instead of a space when writing the DNS addresses in the registry.
Related: Malware Changes Router DNS Settings via Mobile Devices
















