Researchers at Symantec have uncovered a fake app store for Google Android that is hosting malware designed to bilk users out of big bucks.
According to Symantec, mobile malware scammers have created the fake market to host various applications that are actually Trojans used for SMS fraud.
 “We’re still investigating this aspect of the threat, but it appears the creators of the site are driving traffic through a number of means, such as forums, tweets, search results, etc,” said Vikram Thakur, principal security response manager at Symantec.
“We’re still investigating this aspect of the threat, but it appears the creators of the site are driving traffic through a number of means, such as forums, tweets, search results, etc,” said Vikram Thakur, principal security response manager at Symantec.
The company has left the takedown of the site to the “proper authorities,” Thakur said. Meanwhile, the makers of the site are shielding their malware using a tactic frequently found in PC malware attacks – server-side polymorphism. When Symantec downloaded identical copies of applications just minutes apart, researchers noticed the file sizes were drastically different. The reason – the site is using server-side polymorphism to change the content of the package being downloaded in order to evade detection by security software.
“It is also interesting to note that the files not only differ from each other, but that the sizes of all three are much bigger than the old variants used to be,” blogged Symantec threat analyst Joji Hamada. “The older variants may have been in the range of around 50KB – 100KB, but…the size of the files is now in the range of around 1MB. Making the size bigger may be an attempt to look more authentic.”
According to Hamada, the current version of the fake market looks enough like the real Android app store that “if you were not looking at the URL, the average person would probably not be able to tell the difference between the two.”
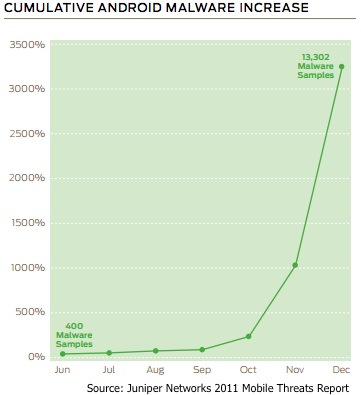
Though much has been written in the past year about the increase of Google Android malware, it should also be noted that many of those infections start with people downloading programs from third-party application stores.
“In some areas, such as China, there is no official Android Market,” noted Tim Armstrong, malware researcher at Kaspersky Lab. “Even so, developers understand that there is money to be made on the platform, and consumers want apps. In other areas, some alternative markets predate the official Android Market, and many apps that are removed from the market for violating the official terms of service stay available on alternate sources (such as tether apps).”
 “We have always recommending sticking to the official channels for apps whenever available,” he added. “Much of the malware we’ve seen so far has arrived via non-market channels. With the addition of app review in the Android Market, we hope it will become an even safer place.”
“We have always recommending sticking to the official channels for apps whenever available,” he added. “Much of the malware we’ve seen so far has arrived via non-market channels. With the addition of app review in the Android Market, we hope it will become an even safer place.”
In some cases, users are required to use third-party markets based on device restrictions, noted Joe Chen, director of engineering for Symantec Security Response. In those situations, users should only download apps from markets hosted by well-known legitimate vendors.
“Beyond that, users should always pay attention to the permissions an app requires before downloading it; if they seem excessive for what the application is designed to do, it would be wise to not install the application,” he said. “Users should also review other users’ comments on the marketplace to assist in determining if an app is safe before downloading. Finally, another tip is to pay attention to the name of the app creator. If downloading a popular app from a well-known app creator, then an app that purports to be the legitimate version, but has a different author listed should be a definite red flag.”












