With Electronic Mail rooms, You Can hold on to Documents Almost Indefinitely, and that Generates a Security Risk.
It may be lost on the user base in which you’ll find the highest percentage of Justin Bieber fans, but no one can deny the importance of email in today’s world. After all, it has revolutionized communication in such a way that it had its effect on the rapid adoption of globalization. Email allows companies to operate all over the world with ease, to communicate both internally and externally regardless of geographical boundaries. Although social networks have won the users’ favor in personal communication, there are still no contenders to the popularity of email in business and even the most hardcore social network users possess an email account, a testimony to its role in everyone’s lives. However, there’s one thing that despite early predictions email has yet been able to do and that is to “kill” regular mail. Receipts, bank statements and many other mail items are still printed out, put into envelopes and delivered by hand to their recipients the old fashioned way, as if the information revolution never happened. “Snail mail” is still alive and kicking, especially in formal communications between companies and their customers.
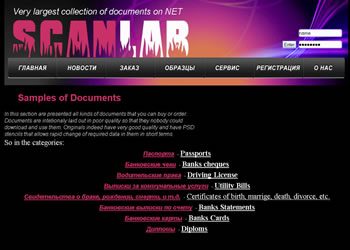
 In general, snail mail is considered to be much more secure than email, and rightly so. Some financial institutions send their customers email notifications of money transfers issued from their accounts. In case of a fraudulent transfer, such a notification may alert the customer of the fraud, who will in turn call the bank and alert them. For fraudsters, the way around the problem is relatively simple. When targeting banks that send these notifications, fraudsters would ask in their phishing scams for the victim’s email address as well as email password. Not surprisingly, the victims are more than willing to provide them. Before issuing the transfer, the fraudsters would log into the account and add a rule that simply deletes any messages coming from the bank. This way, even if the customer receives his email on a mobile device, he still won’t be able to receive the notification and will remain oblivious to the fraudulent activity taking place in his account. One of the great advantages of webmail – being accessible from anywhere in the world – is certainly not adding to its security. Organizations are aware of the gap between the security of snail mail and the security of email, asking in some situations for documents only sent via snail mail, such as bank statements, as a means of validation. Fraudsters that are interested in circumventing this hurdle prefer not to “hack” someone’s physical mailbox, but instead forge the documents altogether. There are multiple services in the underground that offer document forgery services – pick a document, pay the fees and several business days later you should receive the forged document via email for printing.
In general, snail mail is considered to be much more secure than email, and rightly so. Some financial institutions send their customers email notifications of money transfers issued from their accounts. In case of a fraudulent transfer, such a notification may alert the customer of the fraud, who will in turn call the bank and alert them. For fraudsters, the way around the problem is relatively simple. When targeting banks that send these notifications, fraudsters would ask in their phishing scams for the victim’s email address as well as email password. Not surprisingly, the victims are more than willing to provide them. Before issuing the transfer, the fraudsters would log into the account and add a rule that simply deletes any messages coming from the bank. This way, even if the customer receives his email on a mobile device, he still won’t be able to receive the notification and will remain oblivious to the fraudulent activity taking place in his account. One of the great advantages of webmail – being accessible from anywhere in the world – is certainly not adding to its security. Organizations are aware of the gap between the security of snail mail and the security of email, asking in some situations for documents only sent via snail mail, such as bank statements, as a means of validation. Fraudsters that are interested in circumventing this hurdle prefer not to “hack” someone’s physical mailbox, but instead forge the documents altogether. There are multiple services in the underground that offer document forgery services – pick a document, pay the fees and several business days later you should receive the forged document via email for printing.
Just because email hasn’t taken snail mail completely out of our lives, it doesn’t mean there aren’t any additional attempts to do just that. These initiatives use a different approach than email. Instead of replacing snail mail they wish to move it to the web. These services are still uncommon and their market share is quite small, but they are slowly growing in numbers and are backed by powerful entities in the regions in which they operate. Earth Class Mail (ECM) is a company trying to do just that. Founded by several startup junkies, ECM has a digital mailroom which scans physical mail items, making them available to their customers online from any computer. All the customers have to do is to forward their mail to an ECM-supplied address. Another recently launched service is iPost, by the Israeli Post Company. The service, offered for free to any Israeli, allows users to receive certain documents online instead of via their physical mailbox. As the mail items are already processed by the company, no mail forwarding is needed.
One of the advantages of using an online service such as ECM or iPost is that you don’t have to deal with the usual clutter of paper. Once you’ve paid a bill or received an invoice, for how long do you have to hold on to it? On one end, you don’t want to keep every document you’ve ever received. On the other, what would happen if all of a sudden, for whatever reason, you’ll need to look at a bill from 2007?
With electronic mail rooms, there is no problem. As documents can be easily stored in the same place and arranged, you can hold on to documents almost indefinitely, until you run out of mailbox space – and that generates a security risk.
Dumpster diving requires the fraudster to have physical access to the victim’s location, making it hard to target a specific victim whose information was stolen online. In such a case, either the fraudster would have to travel to the victim’s house or the list of potential victims is substantially reduced. In addition, through dumpster diving the fraudster has access only to what the victim has thrown away (which in many cases is enough), but not to what he still has at home. As the documents sent via snail mail are considered by the sender to be more secure than email messages, they may have more sensitive information. Once you place all of them online in one centralized location you’ve basically created a treasure trove for a cybercriminal to hack into and you may run the risk of exposure to “electronic dumpster diving.” Unlike real-world dumpster diving, though, a cybercriminal who manages to access the account would gain access to all the documents currently held by the user, not just those that were thrown away. In that sense, “electronic breaking and entering” would be a much more accurate term, as the fraudster would have to break into the victim’s house to get these documents in the real-world equivalent.
My point is not that Earth Class Mail, iPost or any other similar service are not secure enough. I have not touched on the various security controls that they employ to protect their users, which may be adequate. The point is that as these services pick up traction and gain a large user base they will become a big target for cybercriminals. Phishing, triggers of Trojan Horses and numerous other attacks could be employed to get customers credentials. Any new or existing player in this field will have to take that into consideration and make greater investments in security to protect the users.















