Organizations have been warned that a misconfiguration in Salesforce Communities can lead to the exposure of sensitive information.
While the misconfiguration has been known since at least last year and Salesforce has taken steps to prevent incidents, data security company Varonis says it’s still seeing many affected organizations. Varonis believes thousands of companies could still be vulnerable.
Salesforce Communities enable Salesforce customers to connect and collaborate with employees, partners and customers. These communities are typically indexed by Google, which can be useful to partners and customers, but it can also be useful for attackers looking for organizations they can target.
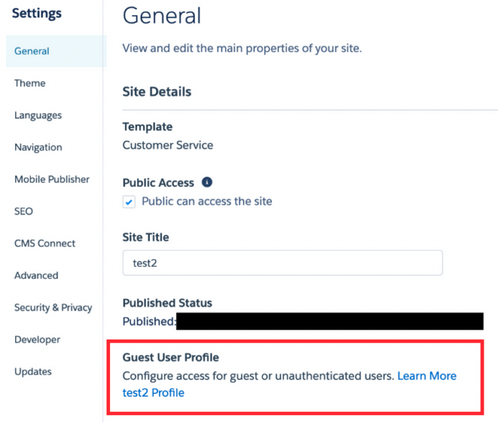
The problem is that some Salesforce Communities are configured to give unauthenticated (guest) users too much access. An attacker can exploit this insecure configuration to query objects that can contain sensitive information.
An attacker can gain access to information such as names, email addresses, customer lists, account records, support data, employee calendars, and other potentially sensitive information about the targeted organization’s clients and operations. Varonis said its researchers discovered “troves of exposed sensitive records.”
The obtained information can be useful for spear-phishing attacks and, in some cases, to infiltrate the system and move laterally, the security firm warned.
“An advanced adversary might try to attack vulnerable custom and 3rd party components,” Varonis said. “In some cases, it is possible to take over the entire Salesforce instance just by exploiting a vulnerable custom Apex class that is exposed to guest users.”
Salesforce administrators have been advised to check settings related to guest permissions and guest user access to avoid such incidents.
Salesforce, which has more than 150,000 customers, including a majority of Fortune 100 companies, took steps last year to reduce the chances of organizations accidentally exposing data through these types of misconfigurations.
However, Varonis has advised Salesforce customers to review their current settings to ensure they don’t expose sensitive information.
Related: Despite Warnings, Cloud Misconfiguration Problem Remains Disturbing
Related: Survey Shows Reasons for Cloud Misconfigurations are Many and Complex
Related: Thousands of Mobile Apps Expose Data via Misconfigured Cloud Containers















