A new financial malware designed to target the customers of South Korean banks has been spotted in the wild by researchers at Trend Micro.
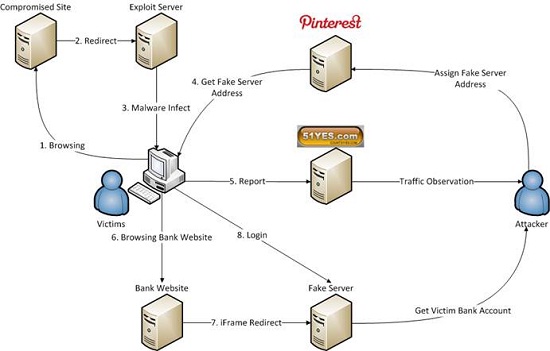
TSPY_BANKER.YYSI, which is part of the BANKER malware family, is being distributed in South Korea with the aid of compromised websites that redirect their visitors to an exploit kit. Once it infects a system, the Trojan monitors victims’ online activities and redirects them to a phishing website when they attempt to access the websites of certain financial institutions.
The malware targets the websites of Hana Bank, Nonghyup Bank, the Industrial Bank of Korea (IBK), Shinhan Bank, Woori Bank, Kookmin Bank, and the Consumer Finance Service Center, Trend Micro said.
When users visit one of these websites, the malware injects an iframe that loads a corresponding phishing page. These phishing sites are designed to look just like the bank’s legitimate website, and the threat is capable of spoofing the URL in the Web browser’s address bar to avoid raising any suspicion.
In addition to the bank websites, TSPY_BANKER.YYSI also targets a popular South Korean search engine. When victims visit this site, they are presented with a pop-up window containing links to the websites of banks monitored by the malware.
The redirection to the phishing pages only occurs when users visit the banking websites with Internet Explorer. However, this isn’t a problem since an outdated South Korean law requires citizens to bank and make online purchases with Internet Explorer. Statistics show that 75% of the country’s Web usage involves this browser.
What’s interesting about TSPY_BANKER.YYSI is that it uses the social media network Pinterest in its command and control (C&C) routines. Instead of contacting a C&C server, the Trojan accesses comments posted on Pinterest. The comments, which look something like “104A149B245C120D,” are decoded (by replacing letters with a dot) and the result is an IP address for the server hosting the phishing page. This tactic allows cybercriminals to quickly change the location of their servers in order to avoid detection, Trend Micro said in a blog post.
In one of the attacks analyzed by the security firm, the attackers leveraged exploits for two patched Internet Explorer vulnerabilities, CVE-2013-2551 and CVE-2014-0322, to deliver the malware. The exploit code is heavily obfuscated, but researchers have determined that it’s similar to Sweet Orange, an exploit kit that has been used in several campaigns over the past period.
This month, the cybercriminals have leveraged the Gongda exploit kit and a Windows vulnerability (CVE-2014-6332) patched by Microsoft last month.
Attribution is usually a difficult task, but in this case, comments found in the exploit code, the URLs of the servers that the malware communicates with, and a service used by the cybercriminals to generate statistics indicate that the attackers are Chinese speakers.
















